[Research News] Security Engineering Laboratory has been approved for publication in The Web Conference (WWW) 2023 paper
- SKKU National Program of Excellence in Software
- Hit877
- 2023-02-01
Security Engineering Laboratory has been approved for publication in The Web Conference (WWW) 2023 paper.
The paper "AppSniffer: Towards Robust Mobile App Fingerprinting Against VPN" by Sanghak Oh and Professor Hyoungshick Kim of the Security Engineering Laboratory has been approved for publication in the Web Conference (WWW) 2023 (https://www2023.thewebconf.org) (BKIF=4). It will also be announced in Texas in the U.S. in April 2023.
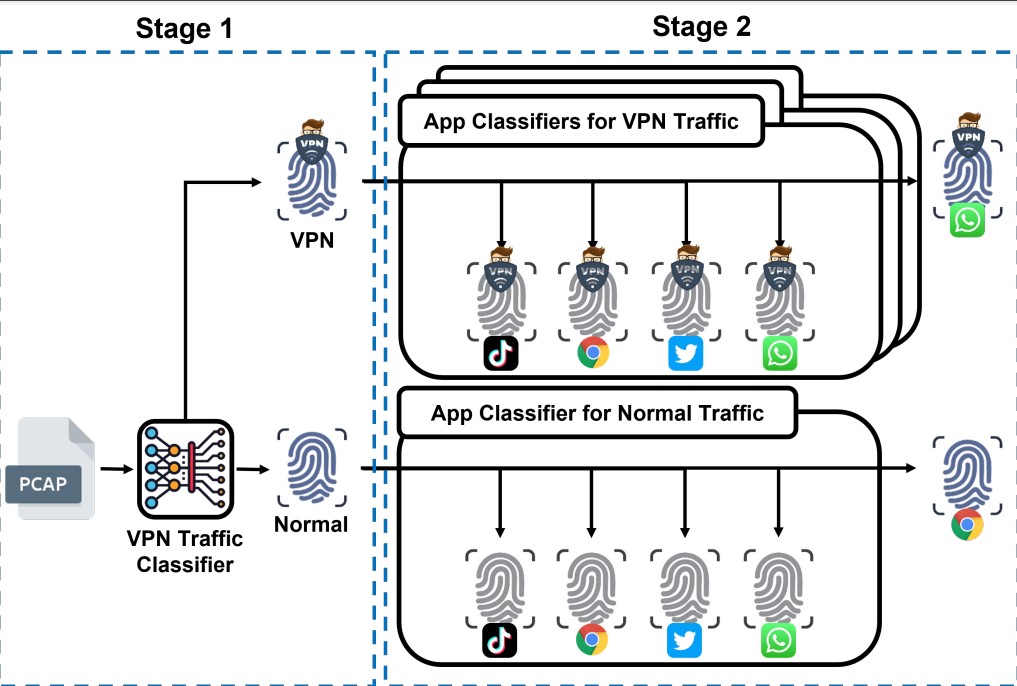
This paper presents the limitation that existing mobile app fingerprinting systems can be easily bypassed through VPN technology through experiments, and proposes AppSniffer, a new mobile app fingerprinting system, to fix this error. AppSniffer is designed to analyze mobile app traffic to extract feature points, even if it is generated in a VPN environment, and finally perform mobile app fingerprinting through ensemble modeling. In this paper, 100 mobile app traffic was collected in both general and VPN environments, and experiments showed that AppSniffer can perform mobile app fingerprinting in all environments (general/VPN environments), showing robustness to VPN traffic.
[Paper information]
Sanghak Oh, Minwook Lee, Hyunwoo Lee, Elisa Bertino, and Hyoungshick Kim. AppSniffer: Towards Robust Mobile App Fingerprinting Against VPN” In Proceedings of the ACM 32nd Web Conference: WWW 2023, Austin, USA, 2023
Abstract: Application fingerprinting is a useful data analysis technique for network administrators, marketing agencies, and security analysts. For example, an administrator can adopt application fingerprinting techniques to determine whether a user's network access is allowed. Several mobile application fingerprinting techniques (e.g., Flowprint, AppScanner, and ET-BERT) were recently introduced to identify applications using the characteristics of network traffic. However, we find that the performance of the existing mobile application fingerprinting systems significantly degrades when a virtual private network (VPN) is used. To address such a shortcoming, we propose a framework dubbed AppSniffer that uses a two-stage classification process for mobile app fingerprinting. In the first stage, we distinguish VPN traffic from normal traffic; in the second stage, we use the optimal model for each traffic type. Specifically, we propose a stacked ensemble model using Light Gradient Boosting Machine (LightGBM) and a FastAI library-based neural network model to identify applications' traffic when a VPN is used. To show the feasibility of AppSniffer, we evaluate the detection accuracy of AppSniffer for 100 popularly used Android apps. Our experimental results show that AppSniffer effectively identifies mobile applications over VPNs with F1-scores between 80.71% and 92.66% across four different VPN protocols. In contrast, the best state-of-the-art method (i.e., AppScanner) demonstrates significantly lower F1-scores between 31.69% and 48.22% in the same settings. Overall, when normal traffic and VPN traffic are mixed, AppSniffer achieves an F1-score of 88.52%, which is significantly better than AppScanner that shows an F1-score of 73.93%.
 김형식 | hyoung@skku.edu | Security Engineering Lab. | http://seclab.skku.edu/
김형식 | hyoung@skku.edu | Security Engineering Lab. | http://seclab.skku.edu/




